Heroes or Hooligans? (Head to Head)
In a moment of total madness, this issue Head to Head decided to handle the ticking parcel bomb that is hacking. After the demise of the old school ‘hacker ethic’ with the rise of off-the-peg hacking tools, who can say what hacking is these days? Equally, since it is possible to find some hackers bending the ear of government and courting big business, while others fall foul of the global crackdown on ‘cybercrime’, it is also unclear who hackers are. In an attempt to completely overload this misfiring signifier, we decided to ask Boris Gröndahl and Pit Schultz to what extent this dark art could be called political. Here’s what they said
Boris Gröndahl - HEAD1
By definition, hacking is as political as playing chess or constructing model railways. The joy of creatively overcoming or circumventing limitations, as one common definition for hacking has it, is not dependent on the character of its limitations, but rather on the challenge of overcoming them. However, hacking does not exist as a pure definition, it exists in real life. The limitations hackers face are not only technological, but also legal, economic, social, and political. At some point all hackers realise that their joy clashes with ‘the command & control structures of the global economy’ – in the form of parents, sysadmins, corporate hierarchies, organised crime, courts and police. This confrontation is inevitable, although to many hackers it comes as a shock. This shock determines to an extent the political mindset of hackers and fosters their proverbial rebellion against rules, structures and authorities – the vulgar anarchism of the lone nerd.
As in rock music, this rebel attitude is not yet politics. You find everything from the ultra-right libertarian crackpot Eric Raymond to leftish hippie-liberal Richard Stallman even in the narrow group of traditional programmer-hackers. The root for both Raymond and Stallman (or, more generally, the Open Source and the Free Software camps) is the same tradition of hacking, based on cooperative coding, free exchange of ideas, and the rejection of the notion of turning software into a scarce resource. But where Stallman sees free software co-operation as a potlatch, a non-market form of exchange, Raymond famously worships it as the bazaar, a generalised market.
Raymond and other cyberlibertarians are indeed true rebels, but they are rebels in the sense of Ayn Rand’s or Joseph Schumpeter’s maverick entrepreneurs, up in arms against outworn corporate rules to create new ones, creatively destroying traditions by employing capitalist market forces. The same dynamics apply for crypto-anarchists, pirates, or any other corner of the hacker movement. In the ‘70s, hackers on the US Defence Department payroll were building the internet, while fellow hackers promoted stealing phone calls by using hacking tools as a way to protest against the US war in Vietnam.
The hacker movement clearly has a right- and a left wing, even though most hackers themselves don’t admit it. The right wing libertarian faction, particularly in the US, blends the anti-authoritarian ethos typical to all hackers, with the strong anti-statist traditions of the political right, from Milton Friedman through to Timothy McVeigh. The left-wing connects to the anti-authoritarian attitudes of post ‘68 movements. Its anti-statism, whilst often naïve, still finds room for the idea of public goods and services, and is more sceptical about the free market. That this faction tends to dominate has a lot to do with its political context. The German Chaos Computer Club, for instance, was conceived on the fringes of the Green movement, and this can still be traced in their political ideas. The line between these factions is at times blurry and you can find many individual hackers on both sides. But I think this further supports the point that hacking may be a great craft, an indispensable tool in the quiver of modern politics, but in itself it’s politically void.
Pit Schultz - HEAD2
In the past, the unsung computer genius from MIT and the suburban teenage villain were both united in the mythic figure of the hacker. Mainstream media represented them as pioneers of a new and ambivalent media freedom. Today, a lot of their powers have shifted to experienced users, anybody can be an expert in a matter of clicks. The antics of adventurous power-users and nasty script kiddies are threatening to replace the codified ethics of traditional hackerdom as it transforms into a new mass media culture.
Hacking as a metaphor for state-of-the-art cultural criticism can feel like a misleading abstraction when you’ve just been hacked. If you haven’t, you’re haunted by the possibility. Hacker tools developed by highly skilled security system experts are available to anyone who can use search engines and are as easy to install and use as virus scanners. There might be a reason why, in times of infowar, software tools can obtain the legal status of weaponry.
 >> Defcon 1, Copyright © 1998, David DittrichLast autumn a number of cultural net projects with a strong dedication to open access and free speech got hacked and their content erased using such tools (SSH Exploits and Linux Root Kits). Among them was the well known open audio archive, Orang, where thousands of audio files got lost. It is quite difficult to find a cultural net project which hasn’t had problems with hackers over the last few months. For most, the damage could be fixed by installing a new system, while others lost unique digital art projects.
>> Defcon 1, Copyright © 1998, David DittrichLast autumn a number of cultural net projects with a strong dedication to open access and free speech got hacked and their content erased using such tools (SSH Exploits and Linux Root Kits). Among them was the well known open audio archive, Orang, where thousands of audio files got lost. It is quite difficult to find a cultural net project which hasn’t had problems with hackers over the last few months. For most, the damage could be fixed by installing a new system, while others lost unique digital art projects.
A cultural bureaucrat will be quick to remind you that a good project manager will have a better back up strategy, but tactical media projects like Orang are rarely realised under proper management regimes. Often they operate with minimal infrastructure but gain momentum nevertheless. In a slick simulation of technological dysfunction, this problem reappears as the aestheticisation of error in the white cube of media art exhibitions. On a machine which is perfectly maintained one can experience artefacts which resemble fatal computer failures. Such taming of the shrew is the opposite of what tactical media is about.
The spiral of technologisation in the security sector goes further. The result is that small providers, self-run co-locations or public access sites of universities and libraries, move over from a policy of an open and free digital commons to a strategy of paranoid enclosure. Meanwhile, the security experts and their service industry prosper. In their midst former hackers, who still perform their sport like innocent boy scouts, are praised by the net culture discourse as role models.
Transmediale 2.0 in Berlin featured a workshop on ‘hacking techniques’ organised by a Spanish art group. Many assumed that it was run by the Chaos Computer Club, a hacker group that participated in the off-programme. Their contribution, Blinkenlights, a popular interactive light installation in urban space and the internet, could easily have won prizes in all the categories grouped under the event’s catchphrase ‘Go Public’. For administrative reasons, it was run out of the competition. The winning entry in the software art prize was itself ‘hacked’ by a guy using a ‘fork bomb’ script as objet-trouvé. A mock US diplomat participated in the official opening ceremony, as one of many carnivalesque pranks. This appropriation of hacking served as a subversive gesture, glossing over the dilution of the political.
As a theoretical reference, Mckenzie Wark’s Hacker Manifesto makes the hacker a hero who inherits an outdated model of traditional criticism. On a popular level, Hollywood movies, and TV documentaries, books and club tracks have featured the hacker as a mediator of life in a digital world. In fact this overworked protagonist with his highly respected skills is being crushed under the burden of carrying media culture’s social interface, its role as a buffer zone between technological modernisation, the conservative agencies of high culture, and the urge of mass media to popularise digital technologies. The parameters of this system closely determine the confines in which media art and discourse can unfold.
The dream of a vital hacker culture, an elite with its own ethics and order, is at an end when anyone can download the skills of generations of hackers in a piece of ordinary code. Once installed on a script kiddy’s PC, all social and cultural knowledge is stripped from the software, and its pure subversive potential can unfold. Call it digital hooliganism, or cyber black bloc, once a software is released only another piece of code can make it stop. While the skills embedded in the code get more and more complex, the skills to run the code zero out. In the end it doesn’t matter if the wizard wears a black or a white hat.
But hacking becomes more than just ‘cool’ in exactly the moment when operation Homeland Security, the law enforcement agencies of international copyright, and new national info-warrior divisions, criminalise and militarise the act of hacking while at the same time thousands of out-of-the-box hackers popularise the practice in countless acts of vandalism. Hacking is more than a metaphor: wherever there’s a hack, a virtual border has been crossed illegally. The erosion of security leads to new models of distribution and storage which make ‘copy me’ an axiom of sustainability. The strongest tools of the web at the moment, peer-to-peer filesharing networks, are built on the principle of open system architectures with minimal access restrictions which puts the power in the hands of the users. Real insecurity is a basic feature of the networked society.
Boris Gröndahl is a journalist in Frankfurt and Berlin
Pit Schultz lives in Berlin and is co-founder of nettime.org, mikro.org, klubradio.de and bootlab.org
[http://www.blinkenlights.de] [http://www.feelergauge.net/projects/hackermanifesto/version_2.0/] [http://astalavista.box.sk]
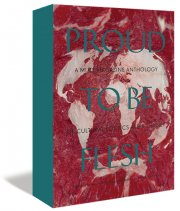
Mute Books Orders
For Mute Books distribution contact Anagram Books
contact@anagrambooks.com
For online purchases visit anagrambooks.com